What Is ISO 27001 Framework?
In an era where data breaches can lead to substantial financial losses, reputational damage, and legal repercussions, ISO 27001 offers a comprehensive blueprint for organizations to manage information security risks proactively. By adhering to ISO 27001 standards, businesses can not only protect their sensitive information but also reassure clients, partners, and stakeholders about their commitment to maintaining the highest standards of data security.
This internationally recognized standard goes beyond being a compliance requirement; it becomes a strategic investment in building trust, ensuring business continuity, and fostering a culture of security awareness. ISO 27001's systematic approach, encompassing risk assessment, controls implementation, and continuous improvement, positions organizations to adapt and thrive in the face of evolving digital threats, thereby future-proofing their operations and ensuring the longevity of their success.
Understanding ISO 27001: The Basics
ISO 27001, formally known as ISO/IEC 27001, is an internationally recognized standard for information security management systems (ISMS). It lays out a systematic approach for organizations to manage and protect their information assets, whether they are electronic, physical, or otherwise. The framework is designed to ensure the confidentiality, integrity, and availability of information while addressing legal, regulatory, and contractual requirements.
ISO 27001 provides a structured methodology that empowers organizations to identify potential security risks, assess their impact, and implement appropriate mitigation controls. By establishing a robust ISMS based on ISO 27001 principles, businesses can create a proactive environment that anticipates and safeguards against evolving cyber threats and vulnerabilities.
This standard encourages a culture of continuous improvement, where regular assessments, audits, and reviews drive the optimization of information security measures. As technology advances and the digital landscape evolves, ISO 27001 remains a steadfast foundation for organizations to navigate the complexities of information security, instilling confidence in stakeholders and enabling secure and resilient operations in an interconnected world.
Key Principles of ISO 27001
- Risk Assessment and Management: One of the fundamental principles of ISO 27001 is the identification and assessment of information security risks. Organizations must conduct a thorough analysis of potential threats and vulnerabilities to their information assets, evaluate the potential impact, and implement appropriate controls to mitigate these risks.
- Top Management Leadership: ISO 27001 emphasizes the involvement of top management in the establishment, implementation, and continual improvement of the ISMS. Leadership commitment ensures that information security becomes an integral part of the organization's culture.
- Continuous Improvement: The ISO 27001 framework follows the Plan-Do-Check-Act (PDCA) cycle, encouraging organizations to continuously monitor and improve their information security practices. This iterative process helps organizations adapt to evolving threats and challenges.
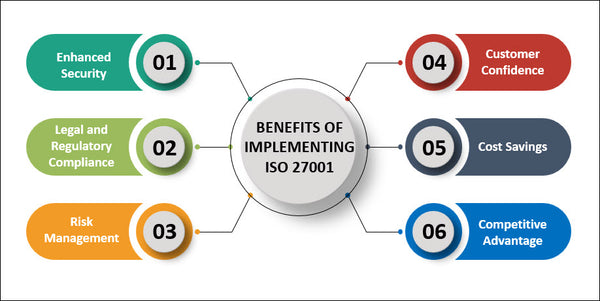
Benefits of Implementing ISO 27001
- Enhanced Security: By implementing ISO 27001, organizations can establish a robust security framework that safeguards against various threats, including cyberattacks, data breaches, and unauthorized access.
- Legal and Regulatory Compliance: ISO 27001 helps organizations stay compliant with relevant laws, regulations, and contractual requirements related to information security.
- Risk Management: The framework's risk assessment and management approach enables organizations to proactively identify and mitigate potential security risks, reducing the likelihood of security incidents.
- Customer Confidence: Achieving ISO 27001 certification demonstrates an organization's commitment to information security, enhancing customer trust and confidence in its ability to protect sensitive data.
- Cost Savings: Effective information security management can lead to cost savings by preventing security breaches, reducing downtime, and avoiding potential legal and financial penalties.
- Competitive Advantage: ISO 27001 certification can provide a competitive advantage, especially when bidding for contracts or partnerships that require robust information security measures.
Implementing ISO 27001: Step-by-Step Guide
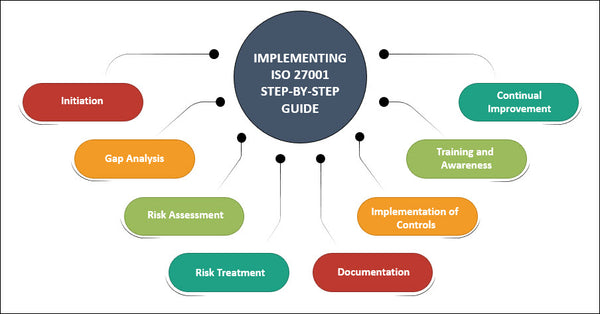
- Initiation: The first step in implementing ISO 27001 is to gain organizational commitment and support from top management. This involves defining the scope of the ISMS and identifying key stakeholders.
- Gap Analysis: Conduct a comprehensive gap analysis to assess the organization's current information security practices against the requirements of ISO 27001. This step helps identify areas that need improvement and informs the development of an action plan.
- Risk Assessment: Identify and assess potential risks to the organization's information assets. Evaluate the impact and likelihood of each risk to prioritize them for mitigation.
- Risk Treatment: Develop and implement risk treatment plans that outline specific controls and measures to mitigate identified risks. These controls can include technical, organizational, and procedural measures.
- Documentation: Documentation in the context of ISO 27001 refers to the organized creation, management, and maintenance of records, policies, procedures, guidelines, and other materials that define an organization's information security management system (ISMS).
- Implementation of Controls: Implement the controls outlined in the risk treatment plans. These controls may include access controls, encryption, incident response procedures, and employee training.
- Training and Awareness: Train employees at all levels on the importance of information security and their roles in maintaining it. Awareness campaigns can help foster a security-conscious organizational culture.
- Performance Evaluation: Performance evaluation within the ISO 27001 framework involves the systematic assessment of an organization's information security management system (ISMS) to gauge its efficiency, effectiveness, and adherence to established objectives and controls.
- Management Review: The ISO 27001 framework's management review is a systematic evaluation conducted by an organization to assess the effectiveness, adequacy, and suitability of its information security management system (ISMS).
- Continual Improvement: Continual improvement, a fundamental principle of ISO 27001, involves the ongoing and systematic enhancement of an organization's information security management system (ISMS).
Conclusion
In today's interconnected and data-driven world, organizations must prioritize information security to protect their valuable assets and maintain the trust of their stakeholders. The ISO 27001 framework provides a structured and comprehensive approach to information security management, helping organizations identify risks, implement controls, and continuously improve their security practices. By adhering to the principles and steps outlined in ISO 27001, organizations can establish a robust information security management system that safeguards against a wide range of threats and enhances their overall resilience in the digital landscape.
Implement ISO Faster with a Complete Documentation System
ISO Toolkit for Your Standard
Pick your toolkit from 8 ready-to-use ISO toolkits available: ISO 27001, 9001, 14001, 45001, 22301, 20000, and 42001 (AI Governance).
✔ Complete ISO documentation framework
✔ Policies, procedures, templates, and records
✔ Risk management & internal audit templates
✔ Management Review and Nonconformance
✔ ISO Standard Mapped Implementation Plan
💡 All toolkits come with instant download, one-time payment, and unlimited email & chat support.
ISO PowerPack Bundle
Designed for teams, organizations, and consultants managing multiple ISO implementations across projects and clients.
✔ Unlimited internal and client use
✔ Deliver ISO services from day one
✔ Impress clients and auditors
✔ Skip months of document creation
✔ Grow your consulting business
💡All the benefits of our ISO toolkits combined in one powerful bundle — save over $1,000 compared to buying the toolkits individually.